

Introducing Quantum Origin
A quantum-enhanced cryptographic key generation platform to protect data from advancing threats
- Quantum Origin is the world’s first commercial product built using quantum computers that delivers an outcome that classical computers could not achieve
- Quantum Origin is the first platform to derive cryptographic keys using the output of a quantum computer to ensure data is protected at foundational level against evolving attacks
- It provides immediate protection to enterprises and governments from current security issues, arising from the use of weaker random number generators (RNGs)
- Quantum Origin also helps protect against ‘hack now, decrypt later’ attacks, which are already happening and will have future implications
- The quantum-enhanced cryptographic keys generated by Quantum Origin are based on verifiable quantum randomness and can be integrated into existing systems. The protocol relies on “entanglement”, a unique feature of quantum mechanics.
- Quantum Origin supports traditional algorithms, such as RSA or AES, as well as post-quantum cryptography algorithms currently being standardized by the National Institute for Standards and Technology (NIST)
Cambridge Quantum (CQ), the global leader in quantum software, and a wholly owned subsidiary of Quantinuum, the world’s leading integrated quantum computing company, is pleased to announce that it is launching Quantum Origin – the world’s first commercially available cryptographic key generation platform based on verifiable quantum randomness. It is the first commercial product built using a noisy, intermediate-scale quantum (NISQ) computer and has been built to secure the world’s data from both current and advancing threats to current encryption.
Randomness is critical to securing current security solutions as well as protecting systems from the future threat of quantum attacks. These attacks will further weaken deterministic methods of random number generation, as well as methods that are not verifiably random and from a quantum source.
Today’s systems are protected by encryption standards such as RSA and AES. Their resilience is based on the inability to “break” a long string from a random number generator (RNG). Today’s RNGs, however, lack true, verifiable randomness; the numbers being generated aren’t as unpredictable as thought, and, as a result, such RNGs have been the point of failure in a growing number of cyber attacks. To add to this, the potential threat of quantum attacks is now raising the stakes further, incentivizing criminals to steal encrypted data passing over the internet, with a view to decrypting it later using quantum computers. So-called “hack now, decrypt later” attacks.
Quantum Origin is a cloud-hosted platform that protects against these current and future threats. It uses the unpredictable nature of quantum mechanics to generate cryptographic keys seeded with verifiable quantum randomness from Quantinuum’s H-Series quantum computers, Powered by Honeywell. It supports traditional algorithms, such as RSA or AES, as well as post-quantum cryptography algorithms currently being standardized by the National Institute for Standards and Technology (NIST).
“We have been working for a number of years now on a method to efficiently and effectively use the unique features of quantum computers in order to provide our customers with a defense against adversaries and criminals now and in the future once quantum computers are prevalent,” said Ilyas Khan, CEO of Quantinuum and Founder of Cambridge Quantum. He added “Quantum Origin gives us the ability to be safe from the most sophisticated and powerful threats today as well threats from quantum computers in the future.”
Duncan Jones, head of cybersecurity at Cambridge Quantum, said: “When we talk about protecting systems using quantum-powered technologies, we’re not just talking about protecting them from future threats. From large-scale takedowns of organizations, to nation state hackers and the worrying potential of ‘hack now, decrypt later’ attacks, the threats are very real today, and very much here to stay. Responsible enterprises need to deploy every defense possible to ensure maximum protection at the encryption level today and tomorrow.”
Quantum-enhanced keys on demand
With Quantum Origin, when an organization requires quantum-enhanced keys to be generated, it can now make a call via an API. Quantum Origin generates the keys before encrypting them with a transport key and securely relaying them back to the organization. To give organizations a high-level of assurance that their encryption keys are as unpredictable as possible, Quantum Origin tests the entire output from the quantum computers, ensuring that each key is seeded from verifiable quantum randomness.
These keys are then simple and easy to integrate within customers' existing systems because they’re provided in a format that can be consumed by traditional cybersecurity systems and hardware. This end-to-end approach ensures key generation is on-demand and is capable of scaling with use, all while remaining secure.
Quantum Origin in practice
Quantum Origin keys should be used in any scenario where there is a need for strong cybersecurity. At launch, Cambridge Quantum will offer Quantum Origin to financial services companies and vendors of cybersecurity products before expanding into other high priority sectors, such as telecommunications, energy, manufacturing, defense and government.
The technology has already been used in a series of projects with launch partners. Axiom Space used Quantum Origin to conduct a test of post-quantum encrypted communication between the ISS and Earth — sending the message “Hello Quantum World” back to earth encrypted with post-quantum keys seeded from verifiable quantum randomness. Fujitsu integrated Quantum Origin into its software-defined wide area network (SDWAN) using quantum-enhanced keys alongside traditional algorithms.
For more information:
— Learn more about Quantum Origin
— Discover our partners
— Explore our case studies
— Book a demo with our experts
About Quantinuum
Quantinuum, the world’s largest integrated quantum company, pioneers powerful quantum computers and advanced software solutions. Quantinuum’s technology drives breakthroughs in materials discovery, cybersecurity, and next-gen quantum AI. With over 500 employees, including 370+ scientists and engineers, Quantinuum leads the quantum computing revolution across continents.

This month, Quantinuum welcomed its global user community to the first-ever Q-Net Connect, an annual forum designed to spark collaboration, share insights, and accelerate innovation across our full-stack quantum computing platforms. Over two days, users came together not only to learn from one another, but to build the relationships and momentum that we believe will help define the next chapter of quantum computing.
Q-Net Connect 2026 drew over 170 attendees from around the world to Denver, Colorado, including representatives from commercial enterprises and startups, academia and research institutions, and the public sector and non-profits - all users of Quantinuum systems.
The program was packed with inspiring keynotes, technical tracks, and customer presentations. Attendees heard from leaders at Quantinuum, as well as our partners at NVIDIA, JPMorganChase and BlueQubit; professors from the University of New Mexico, the University of Nottingham and Harvard University; national labs, including NIST, Oak Ridge National Laboratory, Sandia National Laboratories and Los Alamos National Laboratory; and other distinguished guests from across the global quantum ecosystem.
Congratulations to Q-Net Connect 2026 Award Recipients!
The mission of the Quantinuum Q-Net user community is to create a space for shared learning, collaboration and connection for those who adopt Quantinuum’s hardware, software and middleware platform. At this year’s Q-Net Connect, we awarded four organizations who made notable efforts to champion this effort.
- JPMorganChase received the ‘Guppy Adopter Award’ for their exemplary adoption of our quantum programming language, Guppy, in their research workflows.
- Phasecraft, a UK and US-based quantum algorithms startup, received the ‘Rising Star’ award for demonstrating exceptional early impact and advancing science using Quantinuum hardware, which they published in a December 2025 paper.
- Qedma, a quantum software startup, received the ‘Startup Partner Engagement’ award for their sustained engagement with Quantinuum platforms dating back to our first commercially deployed quantum computer, H1.
- Anna Dalmasso from the University of Nottingham received our ‘New Student Award’ for her impressive debut project on Quantinuum hardware and for delivering outstanding results as a new Q-Net student user.
Congratulations, again, and thank you to everyone who contributed to the success of the first Q-Net Connect!
Become a Q-Net Member
Q-Net offers year‑round support through user access, developer tools, documentation, trainings, webinars, and events. Members enjoy many exclusive benefits, including being the first to hear about exclusive content, publications and promotional offers.
By joining the community, you will be invited to exclusive gatherings to hear about the latest breakthroughs and connect with industry experts driving quantum innovation. Members also get access to Q‑Net Connect recordings and stay connected for future community updates.

In a follow-up to our recent work with Hiverge using AI to discover algorithms for quantum chemistry, we’ve teamed up with Hiverge, Amazon Web Services (AWS) and NVIDIA to explore using AI to improve algorithms for combinatorial optimization.
With the rapid rise of Large Language Models (LLMs), people started asking “what if AI agents can serve as on-demand algorithm factories?” We have been working with Hiverge, an algorithm discovery company, AWS, and NVIDIA, to explore how LLMs can accelerate quantum computing research.
Hiverge – named for Hive, an AI that can develop algorithms – aims to make quantum algorithm design more accessible to researchers by translating high-level problem descriptions in mostly natural language into executable quantum circuits. The Hive takes the researcher’s initial sketch of an algorithm, as well as special constraints the researcher enumerates, and evolves it to a new algorithm that better meets the researcher’s needs. The output is expressed in terms of a familiar programming language, like Guppy or NVIDIA CUDA-Q, making it particularly easy to implement.
The AI is called a “Hive” because it is a collective of LLM agents, all of whom are editing the same codebase. In this work, the Hive was made up of LLM powerhouses such as Gemini, ChatGPT, Claude, Llama, as well as NVIDIA Nemotron, which was accessed through AWS’ Amazon Bedrock service. Many models are included because researchers know that diversity is a strength – just like a team of human researchers working in a group, a variety of perspectives often leads to the strongest result.
Once the LLMs are assembled, the Hive calls on them to do the work writing the desired algorithm; no new training is required. The algorithms are then executed and their ‘fitness’ (how well they solve the problem) is measured. Unfit programs do not survive, while the fittest ones evolve to the next generation. This process repeats, much like the evolutionary process of nature itself.
After evolution, the fittest algorithm is selected by the researchers and tested on other instances of the problem. This is a crucial step as the researchers want to understand how well it can generalize.
In this most recent work, the joint team explored how AI can assist in the discovery of heuristic quantum optimization algorithms, a class of algorithms aimed at improving efficiency across critical workstreams. These span challenges like optimal power grid dispatch and storage placement, arranging fuel inside nuclear reactors, and molecular design and reaction pathway optimization in drug, material, and chemical discovery—where solutions could translate into maximizing operational efficiency, dramatic reduction in costs, and rapid acceleration in innovation.
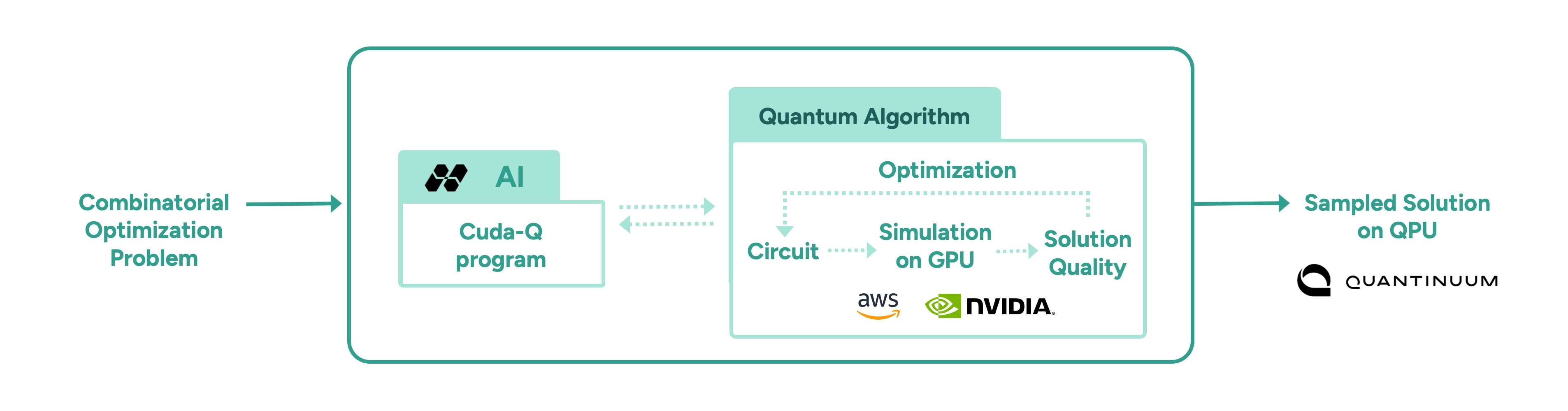
In other AI approaches, such as reinforcement learning, models are trained to solve a problem, but the resulting "algorithm" is effectively ‘hidden’ within a neural network. Here, the algorithm is written in Guppy or CUDA-Q (or Python), making it human-interpretable and easier to deploy on new problem instances.
This work leveraged the NVIDIA CUDA-Q platform, running on powerful NVIDIA GPUs made accessible by AWS. It’s state-of-the art accelerated computing was crucial; the research explored highly complex problems, challenges that lie at the edge of classical computing capacity. Before running anything on Quantinuum’s quantum computer, the researchers first used NVIDIA accelerated computing to simulate the quantum algorithms and assess their fitness. Once a promising algorithm is discovered, it could then be deployed on quantum hardware, creating an exciting new approach for scaling quantum algorithm design.
More broadly, this work points to one of many ways in which classical compute, AI, and quantum computing are most powerful in symbiosis. AI can be used to improve quantum, as demonstrated here, just as quantum can be used to extend AI. Looking ahead, we envision AI evolving programs that express a combination of algorithmic primitives, much like human mathematicians, such as Peter Shor and Lov Grover, have done. After all, both humans and AI can learn from each other.
As quantum computing power grows, so does the difficulty of error correction. Meeting that demand requires tight integration with high-performance classical computing, which is why we’ve partnered with NVIDIA to push the boundaries of real-time decoding performance.
Realizing the full power of quantum computing requires more than just qubits, it requires error rates low enough to run meaningful algorithms at scale. Physical qubits are sensitive to noise, which limits their capacity to handle calculations beyond a certain scale. To move beyond these limits, physical qubits must be combined into logical qubits, with errors continuously detected and corrected in real time before they can propagate and corrupt the calculation. This approach, known as fault tolerance, is a foundational requirement for any quantum computer intended to solve problems of real-world significance.
Part of the challenge of fault tolerance is the computational complexity of correcting errors in real time. Doing so involves sending the error syndrome data to a classical co-processor, solving a complex mathematical problem on that processor, then sending the resulting correction back to the quantum processor - all fast enough that it doesn’t slow down the quantum computation. For this reason, Quantum Error Correction (QEC) is currently one of the most demanding use-cases for tight coupling between classical and quantum computing.
Given the difficulty of the task, we have partnered with NVIDIA, leaders in accelerated computing. With the help of NVIDIA’s ultra-fast GPUs (and the GPU-accelerated BP-OSD decoder developed by NVIDIA as part of NVIDIA CUDA-Q QEC library), we were able to demonstrate real-time decoding of Helios’ qubits, all in a system that can be connected directly to our quantum processors using NVIDIA NVQLink.
While real-time decoding has been demonstrated before (notably, by our own scientists in this study), previous demonstrations were limited in their scalability and complexity.
In this demonstration, we used Brings’ code, a high-rate code that is possible with our all-to-all connectivity, to encode our physical qubits into noise-resilient logical qubits. Once we had them encoded, we ran gates as well as let them idle to see if we could catch and correct errors quickly and efficiently. We submitted the circuits via both NVIDIA CUDA-Q as well as our own Guppy language, underlining our commitment to accessible, ecosystem-friendly quantum computing.
The results were excellent: we were able to perform low-latency decoding that returned results in the time we needed, even for the faster clock cycles that we expect in future generation machines.
A key part of the achievement here is that we performed something called “correlated” decoding. In correlated decoding, you offload work that would normally be performed on the QPU onto the classical decoder. This is because, in ‘standard’ decoding, as you improve your error correction capabilities, it takes more and more time on the QPU. Correlated decoding elides this cost, saving QPU time for the tasks that only the quantum computer can do.
Stay tuned for our forthcoming paper with all the details.