

The Role of Technology Vendors in Your Quantum-Safe Migration
Who is responsible for migrating your systems to quantum-safe algorithms? Is it your vendors or your cybersecurity team?
The customers I speak to are not always clear on this question. But from my perspective, the answer is your cybersecurity team. They have the ultimate responsibility of ensuring your organization is secure in a post-quantum future. However, they will need a lot of help from your technology vendors.
This article outlines what you should expect (or demand) from your vendors, and what remains the responsibility of your cyber team.
What To Expect From General Vendors
A general vendor does not offer specific cryptographic services to you. Instead, they provide a business service that uses cryptography to maintain security and resilience.
Consider the accounting platform SAP. It is no doubt riddled with cryptography, yet its purpose is to manage your finances. Therefore, SAP’s focus will be on migrating their underlying cryptography to post-quantum technologies, while maintaining your business services without interruption.
You should expect a general vendor to share a quantum-safe migration roadmap with you, complete with timelines. They should explain the activities they will complete to address the quantum threat, and how they will impact you as a user.
Although your vendor will not begin migration until the NIST post-quantum algorithms are standardised next year, you should expect them to already have a roadmap in place. If they don’t, this is a cause for concern.
Some vendors may already offer a test version of their product, which uses post-quantum algorithms. This allows your cyber team to experiment with the impact on performance or interoperability.
What To Expect From Cryptographic Vendors
A cryptographic vendor provides you with services directly related to cryptography, such as network security, data encryption or key management.
The expectations that apply to general vendors also apply to cryptographic vendors. However, you will need more information from your cryptographic vendors to pull off a smooth migration.
Cryptographic vendors must provide you with detailed guidance on how to migrate between their current product suite and the new versions that use post-quantum algorithms. For instance, you might need to understand how to re-process legacy data so that it’s protected by the new algorithms. Similarly, network security vendors will need to provide detailed instructions on migrating traffic flows while maintaining uptime.
I would expect cryptographic vendors to be far more hands-on during your migration. Expect to have discussions of your deployment architecture with their account management teams, and don’t be afraid to ask the hard technical questions.
What Information You Should be Ready to Share
The flow of information will not be one-way. You should be prepared to share information with your vendors to help them help you.
Having your migration plan developed, at least at a high level, will be critical for meaningful conversations with your vendors. This will allow you to contrast their timelines for migration versus your expectations.
Vendors will also benefit from understanding how you use their products in conjunction with products from other vendors. The goal here is to spot edge cases, where you risk business downtime because the vendor wasn’t anticipating how you were using their product.
Finally, make sure you know the configuration of your deployment. The devil is in the details when it comes to planning migration, so be prepared to tell your vendor which features you are using and how you’ve configured product security settings.
What is Out of Scope for Your Vendor?
While your vendors should provide a lot of help and guidance, they are not responsible for everything.
Your cybersecurity team will be responsible for planning your overall migration strategy, including prioritising which systems to migrate first. This will involve understanding the relative importance of business systems, and the requirements for data security.
While vendors should provide some guidance for interoperability, ultimately the IT and cybersecurity teams are responsible for ensuring updates to one service do not impact another service.
Finally, you must ensure your IT and cyber teams are leading the conversation with your end users. You cannot rely on vendors to manage the communication with your customers and internal stakeholders.
What Should You Expect to See Today?
A good vendor will already be talking to you about their plans for quantum-safe migration.
For mass-market products, this might be via blog posts and thought-leadership articles. For products with a deeper client/vendor relationship, the topic of quantum-safe migration should already be appearing in quarterly business reviews.
For cryptographic vendors, you should also be expecting test versions to be available today, to allow for experimentation.
Overall, if any vendor is not able to talk about their plans for quantum-safe migration today, even at a high level, then you should flag this as a cause for concern.
About Quantinuum
Quantinuum, the world’s largest integrated quantum company, pioneers powerful quantum computers and advanced software solutions. Quantinuum’s technology drives breakthroughs in materials discovery, cybersecurity, and next-gen quantum AI. With over 500 employees, including 370+ scientists and engineers, Quantinuum leads the quantum computing revolution across continents.
- University of Southern Denmark (SDU) to use Quantinuum Helios, supported by the Danish e-Infrastructure Consortium (DeiC)
- Access to Helios enables SDU to test and refine fault-tolerant algorithms and error-correction codes under realistic hardware conditions
- The collaboration supports at a scale of 48 logical qubits, positioning Denmark at the forefront of scalable, practical quantum computing
- Researchers exploring the scientific foundations for future development of applications in fields including pharmaceuticals, finance, and defense
Progress in quantum computing is measured by hardware advances plus the algorithms and quantum error-correction codes that turn quantum systems into useful computational tools.
Thanks to recent hardware advances, researchers are increasingly sharpening their tools to probe the performance of quantum algorithms and understand how they behave in realistic conditions – where stability, system architecture and algorithm design all shape performance.
A new Denmark-based collaboration between the University of Southern Denmark (SDU), Quantinuum, and the Danish e-Infrastructure Consortium (DeiC) will utilize Quantinuum Helios. Researchers at the SDU’s Centre for Quantum Mathematics, led by Jørgen Ellegaard Andersen, will use Helios to pursue research into topological quantum computing.
Their work could help explain how and why successful quantum algorithms perform as they do, informing the development of high-performance algorithms suited to emerging quantum systems. They’re exploring the scientific foundations that support future quantum applications across areas including pharmaceuticals, finance, and defense.
“We are thrilled to gain access to Quantinuum’s high-fidelity Helios system. This collaboration gives us a unique opportunity to test the limits of our algorithms and evaluate system performance, while advancing fundamental research and laying the foundation for future applications.”
— Professor Jørgen Ellegaard Andersen, Director of the Centre for Quantum Mathematics at University of Southern Denmark
Why topological methods matter
Topological quantum computing is an area of research that connects quantum computation with deep mathematical structures. It includes the study of error correcting codes known as surface codes that encode quantum information in the global properties of systems of logical qubits.
The research team will explore how these codes behave, and how they may support the development of fault-tolerant quantum algorithms in practical implementations under realistic conditions.
This distinction between theory and practical implementation matters. In theory, topological approaches offer a rich framework for designing algorithms and error-correcting codes. In practice, researchers need to understand how those ideas perform when implemented on real systems, where questions of noise, stability, overhead, and scaling become central. The collaboration will allow the SDU team to investigate these questions directly.
New ways to benchmark quantum processors
Beyond individual algorithms and codes, the research will also develop tools for benchmarking quantum processors. The goal is to develop new ways to characterize fidelity and stability in regimes that can be difficult to access.
The team will also explore hybrid quantum–classical approaches, including machine-learning techniques assisted by quantum hardware, to study the mathematical structures at the heart of topological quantum computing. This work reflects a broader field of research in which quantum and classical methods are used together, each contributing to parts of a computational problem.
Strengthening Denmark’s quantum ecosystem
The collaboration reflects the growing role of national quantum infrastructure in supporting research and talent development. Denmark has a long tradition of scientific innovation, and this collaboration is intended to support the country’s continued development in quantum technology.
The initiative is supported by DeiC, which played a central role in securing funding and enabling access to Quantinuum’s systems. DeiC has been assigned a particular role in developing and coordinating quantum infrastructure initiatives for the benefit of universities and industry, operating without its own commercial, sectoral, or geographical interests. This includes securing dedicated access to quantum computers, producing advisory services and supporting the development of new talent in the Danish quantum sector.
“DeiC’s special effort to secure funding and access for this research initiative is rooted in our organization’s role in relation to the Danish Government’s strategy for quantum technology.”
— Henrik Navntoft Sønderskov, Head of Quantum at Danish e-Infrastructure Consortium
This collaboration promises to accelerate the development of practical algorithms. It is grounded in fundamental science – but its focus is practical: discovering and testing mathematical approaches to topological quantum computing that can be implemented, evaluated, and improved on real quantum hardware.
That work requires both theoretical insight and access to a system such as Helios capable of supporting meaningful scientific work.

This month, Quantinuum welcomed its global user community to the first-ever Q-Net Connect, an annual forum designed to spark collaboration, share insights, and accelerate innovation across our full-stack quantum computing platforms. Over two days, users came together not only to learn from one another, but to build the relationships and momentum that we believe will help define the next chapter of quantum computing.
Q-Net Connect 2026 drew over 170 attendees from around the world to Denver, Colorado, including representatives from commercial enterprises and startups, academia and research institutions, and the public sector and non-profits - all users of Quantinuum systems.
The program was packed with inspiring keynotes, technical tracks, and customer presentations. Attendees heard from leaders at Quantinuum, as well as our partners at NVIDIA, JPMorganChase and BlueQubit; professors from the University of New Mexico, the University of Nottingham and Harvard University; national labs, including NIST, Oak Ridge National Laboratory, Sandia National Laboratories and Los Alamos National Laboratory; and other distinguished guests from across the global quantum ecosystem.
Congratulations to Q-Net Connect 2026 Award Recipients!
The mission of the Quantinuum Q-Net user community is to create a space for shared learning, collaboration and connection for those who adopt Quantinuum’s hardware, software and middleware platform. At this year’s Q-Net Connect, we awarded four organizations who made notable efforts to champion this effort.
- JPMorganChase received the ‘Guppy Adopter Award’ for their exemplary adoption of our quantum programming language, Guppy, in their research workflows.
- Phasecraft, a UK and US-based quantum algorithms startup, received the ‘Rising Star’ award for demonstrating exceptional early impact and advancing science using Quantinuum hardware, which they published in a December 2025 paper.
- Qedma, a quantum software startup, received the ‘Startup Partner Engagement’ award for their sustained engagement with Quantinuum platforms dating back to our first commercially deployed quantum computer, H1.
- Anna Dalmasso from the University of Nottingham received our ‘New Student Award’ for her impressive debut project on Quantinuum hardware and for delivering outstanding results as a new Q-Net student user.
Congratulations, again, and thank you to everyone who contributed to the success of the first Q-Net Connect!
Become a Q-Net Member
Q-Net offers year‑round support through user access, developer tools, documentation, trainings, webinars, and events. Members enjoy many exclusive benefits, including being the first to hear about exclusive content, publications and promotional offers.
By joining the community, you will be invited to exclusive gatherings to hear about the latest breakthroughs and connect with industry experts driving quantum innovation. Members also get access to Q‑Net Connect recordings and stay connected for future community updates.

In a follow-up to our recent work with Hiverge using AI to discover algorithms for quantum chemistry, we’ve teamed up with Hiverge, Amazon Web Services (AWS) and NVIDIA to explore using AI to improve algorithms for combinatorial optimization.
With the rapid rise of Large Language Models (LLMs), people started asking “what if AI agents can serve as on-demand algorithm factories?” We have been working with Hiverge, an algorithm discovery company, AWS, and NVIDIA, to explore how LLMs can accelerate quantum computing research.
Hiverge – named for Hive, an AI that can develop algorithms – aims to make quantum algorithm design more accessible to researchers by translating high-level problem descriptions in mostly natural language into executable quantum circuits. The Hive takes the researcher’s initial sketch of an algorithm, as well as special constraints the researcher enumerates, and evolves it to a new algorithm that better meets the researcher’s needs. The output is expressed in terms of a familiar programming language, like Guppy or NVIDIA CUDA-Q, making it particularly easy to implement.
The AI is called a “Hive” because it is a collective of LLM agents, all of whom are editing the same codebase. In this work, the Hive was made up of LLM powerhouses such as Gemini, ChatGPT, Claude, Llama, as well as NVIDIA Nemotron, which was accessed through AWS’ Amazon Bedrock service. Many models are included because researchers know that diversity is a strength – just like a team of human researchers working in a group, a variety of perspectives often leads to the strongest result.
Once the LLMs are assembled, the Hive calls on them to do the work writing the desired algorithm; no new training is required. The algorithms are then executed and their ‘fitness’ (how well they solve the problem) is measured. Unfit programs do not survive, while the fittest ones evolve to the next generation. This process repeats, much like the evolutionary process of nature itself.
After evolution, the fittest algorithm is selected by the researchers and tested on other instances of the problem. This is a crucial step as the researchers want to understand how well it can generalize.
In this most recent work, the joint team explored how AI can assist in the discovery of heuristic quantum optimization algorithms, a class of algorithms aimed at improving efficiency across critical workstreams. These span challenges like optimal power grid dispatch and storage placement, arranging fuel inside nuclear reactors, and molecular design and reaction pathway optimization in drug, material, and chemical discovery—where solutions could translate into maximizing operational efficiency, dramatic reduction in costs, and rapid acceleration in innovation.
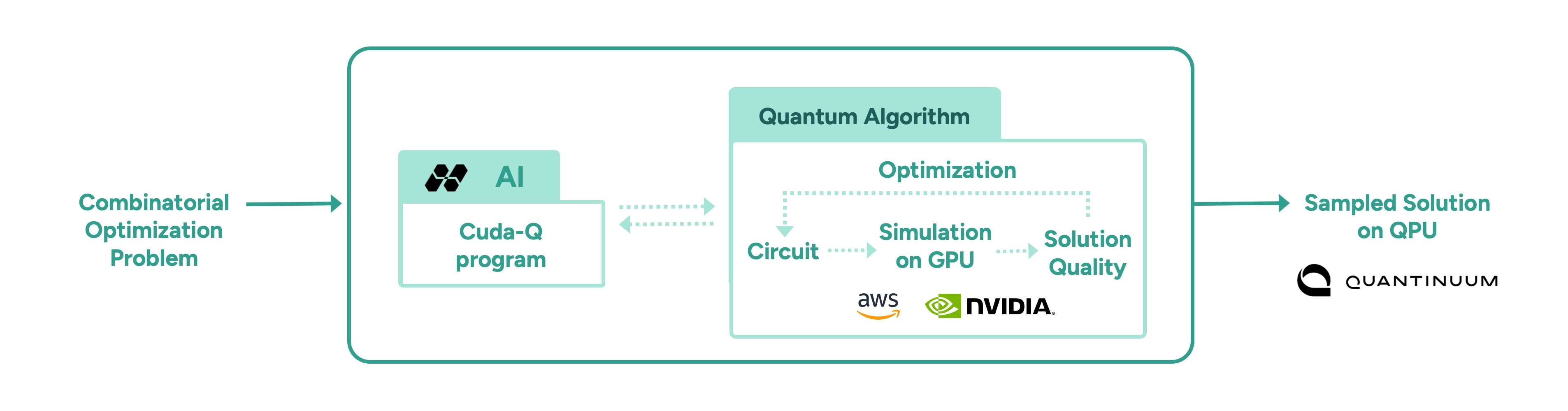
In other AI approaches, such as reinforcement learning, models are trained to solve a problem, but the resulting "algorithm" is effectively ‘hidden’ within a neural network. Here, the algorithm is written in Guppy or CUDA-Q (or Python), making it human-interpretable and easier to deploy on new problem instances.
This work leveraged the NVIDIA CUDA-Q platform, running on powerful NVIDIA GPUs made accessible by AWS. It’s state-of-the art accelerated computing was crucial; the research explored highly complex problems, challenges that lie at the edge of classical computing capacity. Before running anything on Quantinuum’s quantum computer, the researchers first used NVIDIA accelerated computing to simulate the quantum algorithms and assess their fitness. Once a promising algorithm is discovered, it could then be deployed on quantum hardware, creating an exciting new approach for scaling quantum algorithm design.
More broadly, this work points to one of many ways in which classical compute, AI, and quantum computing are most powerful in symbiosis. AI can be used to improve quantum, as demonstrated here, just as quantum can be used to extend AI. Looking ahead, we envision AI evolving programs that express a combination of algorithmic primitives, much like human mathematicians, such as Peter Shor and Lov Grover, have done. After all, both humans and AI can learn from each other.